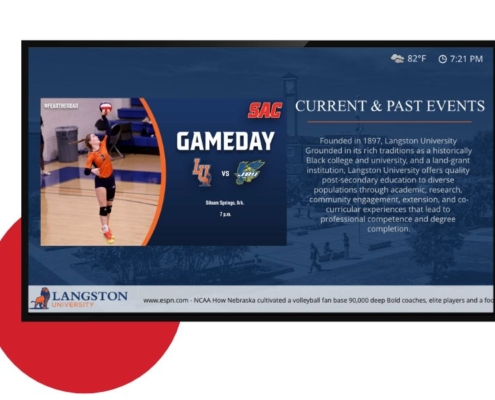
The Comprehensive Benefits of Digital Signage for Business
In today's competitive market, businesses constantly seek innovative ways to improve communication and engagement with their patrons. Digital signage has emerged as a powerful tool to achieve these goals, offering a dynamic platform for advertising,…

Benefits of Remote Guard Services for Remote Locations with Automatic Gates
Remote locations often pose unique security challenges, especially when they require after-hours access without an on-site attendant. Remote guard services have revolutionized the way these sites are monitored and managed, providing efficient,…

Why Choose a Boutique Central Monitoring Station: 10 Reasons It Might Be the Better Choice for Your Home or Business
In the realm of security, selecting the right central monitoring station is paramount. While larger national stations offer extensive resources, boutique monitoring stations provide unique advantages that can be more suitable for some homes…

Advances in Video Surveillance for Remote Locations: Solar Power and Cellular Communication
In recent years, advances in technology have revolutionized video surveillance, making it feasible to monitor remote locations that lack access to traditional power sources and internet connectivity. The combination of solar power and cellular…

Top 10 Advances in Electronic Security to Delay and Deter Potential Active Shooters
In an era where school safety is a paramount concern, the integration of advanced electronic security measures has become crucial in safeguarding students, teachers, and staff. These technologies not only help delay or deter potential active…

Ionization vs. Photoelectric Smoke Detectors
Smoke detectors are essential devices for ensuring the safety of your home and loved ones. They provide early warning in the event of a fire, allowing occupants to evacuate quickly and potentially save lives. However, with different types of…

Unveiling the Top 5 Benefits of Alarm.com’s New Exterior Drone Partnership with Sunflower Labs
Last week at ISC West, the world's leading security industry event, Alarm.com made waves with the announcement of an exciting new partnership with Sunflower Labs, unveiling their groundbreaking Exterior Drone. This collaboration between two…

How Security Foggers Secure Your World
In the realm of security technology, there exists a powerful guardian that operates beyond the conventional realm of alarms and surveillance cameras. It's a revolutionary tool known as a security fogger, and it's transforming the landscape of…

Understanding the Four Levels of Safe Haven Safety Glass for Homes and Businesses
In the realm of home and business safety, the importance of reliable glass solutions cannot be overstated. From protecting against break-ins to mitigating damage from natural disasters, investing in high-quality safety glass is a proactive step…

Lone Worker Safety Device
Lone workers are individuals who perform their job duties in isolation, in remote areas without direct supervision or immediate assistance from colleagues. They face various challenges, such as limited support, increased risk of accidents,…

Gun Shot Detection
Ensuring public safety is increasingly challenging as the specter of an active shooter looms over various settings, burdening business owners, event planners, and government authorities alike.
Gunfire detection systems, also known as gunfire…

The importance of Fleet Vehicle Tracking
Harnesses the power of GPS, vehicle diagnostics, and driver rewards to create a fleet tracking system that not only does the job, but makes everybody’s job easier to do. Safety, accountability, and efficiency are gained at every turn. From…





